12 KiB
lab
| lab | ||||
|---|---|---|---|---|
|
Lab 02b - Manage Governance via Azure Policy
Lab requirements
This lab requires an Azure subscription. Your subscription type may affect the availability of features in this lab. You may change the region, but the steps are written using East US.
Estimated timing: 30 minutes
Interactive lab simulation
An interactive lab simulation is available for this topic. The simulation lets you to click through a similar scenario at your own pace. There are differences between the interactive simulation and this lab, but the core concepts and ideas being demonstrated are the same. An Azure subscription is not required.
Lab scenario
Your organization's cloud footprint has grown considerably in the last year. During a recent audit, you discovered a substantial number of resources that do not have a defined owner, project, or cost center. In order to improve management of Azure resources in your organization, you decide to implement the following functionality:
-
apply resource tags to attach important metadata to Azure resources
-
enforce the use of resource tags for new resources by using Azure policy
-
update existing resources with resource tags
Tasks
- Task 1: Create and assign tags via the Azure portal
- Task 2: Enforce tagging via an Azure Policy
- Task 3: Apply tagging via an Azure Policy
Architecture diagram
Task 1: Assign tags via the Azure portal
In this task, you will create and assign a tag to an Azure resource group via the Azure portal. Tags are a critical component of a governance strategy as outlined by the Microsoft Well-Architected Framework and Cloud Adoption Framework. Tags can allow you to quickly identify resource owners, sunset dates, group contacts, and other name/value pairs that your organinzation deems important. For this exercise, you will assign a tag identifying the resource role ('Infra' for 'Infrastructure').
-
Sign in to the Azure portal -
http://portal.azure.com. -
Search for and select Resource groups.
-
From the Resource groups, select Create.
-
Provide the name
az104-rg2band ensure that the Region is set to East US. -
Click Review + Create, and then click Create.
-
After the resource group is deployed, select Go to resource group, or navigate to the newly created resource group.
-
On the resource group blade, click Tags in the left menu and create a new tag.
-
Create a tag with the following settings and apply your change:
Setting Value Name RoleValue Infra -
Click Apply. You have now manually added a tag to a resource group.
Task 2: Enforce tagging via an Azure Policy
In this task, you will assign the built-in Require a tag and its value on resources policy to the resource group and evaluate the outcome. Azure Policy can be used to enforce configuration, and in this case, governance, to your Azure resources.
-
In the Azure portal, search for and select Policy.
-
In the Authoring section, click Definitions. Take a moment to browse through the list of built-in policy definitions that are available for you to use. List all built-in policies that involve the use of tags by selecting the Tags entry (and de-selecting all other entries) in the Category drop-down list. It might also help to search for
Require a tag. -
Click the entry representing the Require a tag and its value on resources built-in policy and review its definition.
-
On the Require a tag and its value on resources built-in policy definition blade, click Assign.
-
Specify the Scope by clicking the ellipsis button and selecting the following values:
Setting Value Subscription your subscription Resource Group az-rg2b Note
: A scope determines the resources or resource groups where the policy assignment takes effect. You could assign policies on the management group, subscription, or resource group level. You also have the option of specifying exclusions, such as individual subscriptions, resource groups, or resources (depending on the assignment scope).
-
Configure the Basics properties of the assignment by specifying the following settings (leave others with their defaults):
Setting Value Assignment name Require Cost Center tag with Default valueDescription Require Cost Center tag with default value for all resources in the resource groupPolicy enforcement Enabled Note
: The Assignment name is automatically populated with the policy name you selected, but you can change it. The Description is optional. Assigned by is automatically populated based on the user name creating the assignment.
-
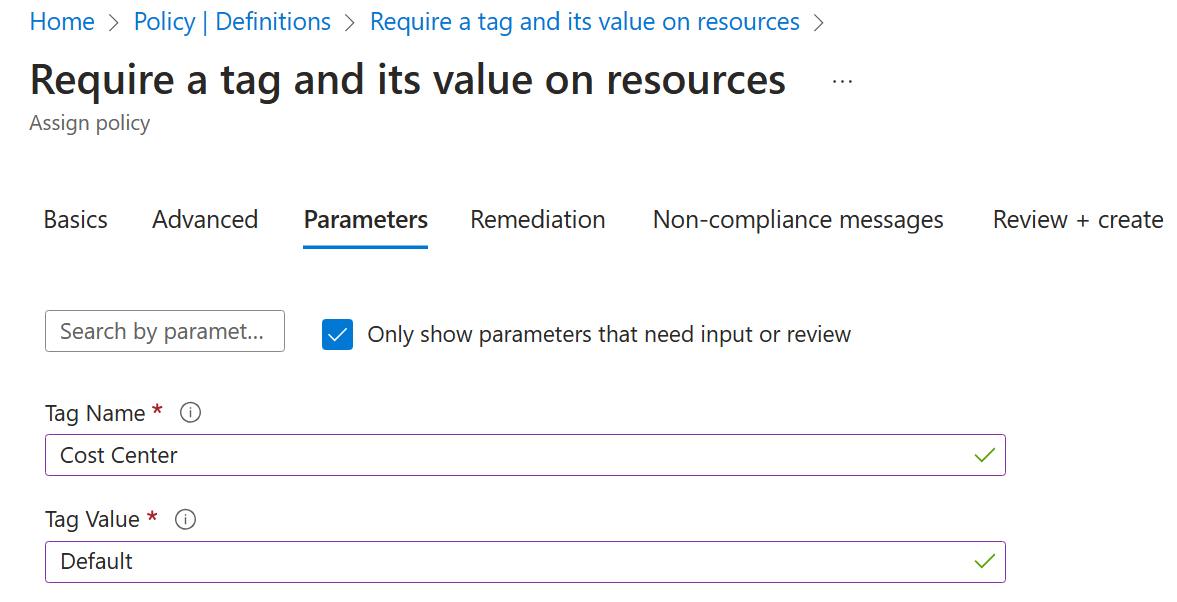
Click Next twice and set Parameters to the following values:
Setting Value Tag Name Cost CenterTag Value Default -
Click Next and review the Remediation tab. Leave the Create a Managed Identity checkbox unchecked.
Note
: This setting can be used when the policy or initiative includes the deployIfNotExists or Modify effect.
-
Click Review + Create and then click Create.
Note
: Now you will verify that the new policy assignment is in effect by attempting to create another Azure Storage account in the resource group without explicitly adding the required tag.
Note
: It might take between 5 and 15 minutes for the policy to take effect.
-
Navigate back to the blade of the resource group that you created in the previous task, and select the Tags blade.
-
On the resource group blade, click + Create and then search for Storage Account, and click + Create.
-
On the Basics tab of the Create storage account blade, verify that you are using the resource group that the policy was applied to and specify the following settings (leave others with their defaults), click Review and then click Create:
Setting Value Resource group az104-rg2b Storage account name any globally unique combination of between 3 and 24 lower case letters and digits, starting with a letter Note
: You may receive a Validation failed. Click here for details error. If so, click the error message to identify the reason for the failure and skip the next step.
-
Once you create the deployment, you should see the Deployment failed message in the Notifications list of the portal. From the Notifications list, navigate to the deployment overview and click the Deployment failed. Click here for details message to identify the reason for the failure.
Note
: Verify whether the error message states that the resource deployment was disallowed by the policy.
Note
: By clicking the Raw Error tab, you can find more details about the error, including the name of the role definition Require Cost Center tag with Default value. The deployment failed because the storage account you attempted to create did not have a tag named Cost Center with its value set to Default.
Task 3: Apply tagging via an Azure policy
In this task, we will use a new policy definition to remediate any non-compliant resources. This will use a remedation task as part of the policy to modify existing resources to be compliant with the policy. In this scenario, we will make any child resources of a resource group inherit the Role tag that was defined on the resource group.
-
In the Azure portal, search for and select Policy.
-
In the Authoring section, click Assignments.
-
In the list of assignments, click the ellipsis icon in the row representing the Require Cost Center tag with Default value policy assignment and use the Delete assignment menu item to delete the assignment.
-
Click Assign policy and specify the Scope by clicking the ellipsis button and selecting the following values:
Setting Value Subscription the name of the Azure subscription you are using in this lab Resource Group the name of the resource group containing the Cloud Shell account you identified in the first task -
To specify the Policy definition, click the ellipsis button and then search for and select
Inherit a tag from the resource group if missing. -
Configure the remaining Basics properties of the assignment by specifying the following settings (leave others with their defaults):
Setting Value Assignment name Inherit the Role tag and its Infra value from the resource group if missing Description Inherit the Role tag and its Infra value from the resource group if missing Policy enforcement Enabled -
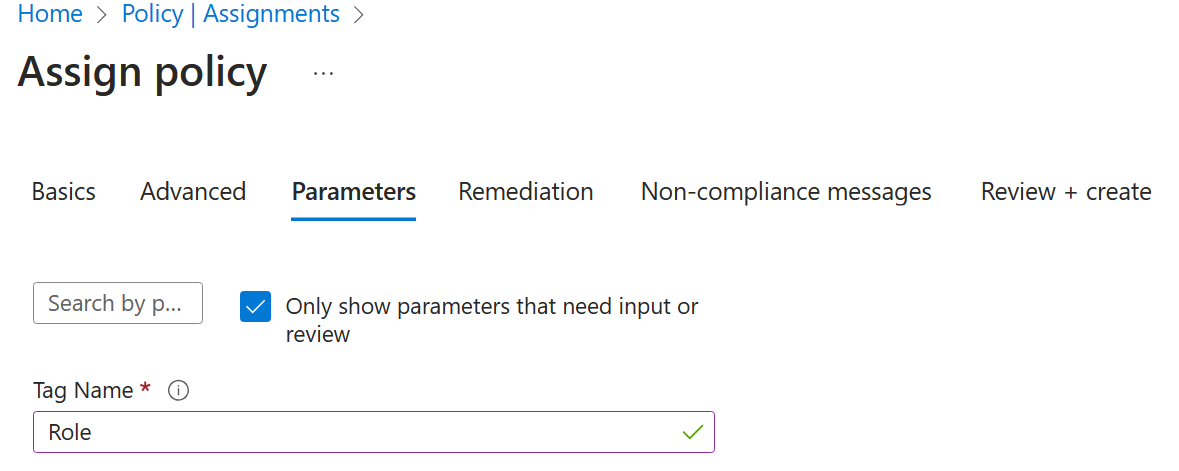
Click Next twice and set Parameters to the following values:
Setting Value Tag Name Role -
Click Next and, on the Remediation tab, configure the following settings (leave others with their defaults):
Setting Value Create a remediation task enabled Policy to remediate Inherit a tag from the resource group if missing Note
: This policy definition includes the Modify effect.
-
Click Review + Create and then click Create.
Note
: To verify that the new policy assignment is in effect, you will create another Azure storage account in the same resource group without explicitly adding the required tag.
Note
: It might take between 5 and 15 minutes for the policy to take effect.
-
Navigate back to the blade of the resource group that you created in the first task.
-
On the resource group blade, click + Create and then search for Storage Account, and click + Create.
-
On the Basics tab of the Create storage account blade, verify that you are using the Resource Group that the Policy was applied to and specify the following settings (leave others with their defaults) and click Review:
Setting Value Storage account name any globally unique combination of between 3 and 24 lower case letters and digits, starting with a letter -
Verify that this time the validation passed and click Create.
-
Once the new storage account is provisioned, click Go to resource button. On the Overview blade, note that the tag Role with the value Infra has been automatically assigned to the resource.
Review
Congratulations on completing the lab. The main takeaways from the lab are:
- Azure tags are metadata that consists of a key-value pair. Tags describe a particular resource in your environment. In particular, tagging in Azure enables you to label your resources in a logical manne.
- Azure Policy establishes conventions for resources. Policy definitions describe resource compliance conditions and the effect to take if a condition is met. A condition compares a resource property field or a value to a required value. There are many built-in policy definitions.
- The Azure Policy remediation task feature is used to bring resources into compliance based on a definition and assignment. Resources that are non-compliant to a modify or deployIfNotExist definition assignment, can be brought into compliance using a remediation task.